Difference between revisions of "Using machine learning to find anomalies in fieldbus networks"
(→Analyser-Output added) |
(→Licence added) |
||
| (One intermediate revision by the same user not shown) | |||
| Line 45: | Line 45: | ||
[[File:Dataset-1-unusual-unknown-addresses.png|200px|middle]] | [[File:Dataset-1-unusual-unknown-addresses.png|200px|middle]] | ||
| − | ==Dataset 2== | + | ==Dataset 2 - Analysers== |
The figures are in the following order: Entropy Analyser | Local Outlier Factor Analyser | Overall Outliers | Support Vector Machine Analyser | Telegram Count | Unknown Address Analyser | The figures are in the following order: Entropy Analyser | Local Outlier Factor Analyser | Overall Outliers | Support Vector Machine Analyser | Telegram Count | Unknown Address Analyser | ||
| Line 55: | Line 55: | ||
[[File:Dataset-2-telegram-count.png|200px|middle]] | [[File:Dataset-2-telegram-count.png|200px|middle]] | ||
[[File:Dataset-2-unknown-addresses.png|200px|middle]] | [[File:Dataset-2-unknown-addresses.png|200px|middle]] | ||
| + | |||
| + | ==Dataset 2 - Log Analysis== | ||
| + | |||
| + | In the following two pdf-files a distribution of telegrams over time (weekday and hour of the day) can be found: | ||
| + | |||
| + | [[File:Dataset-2-telegrams-per-hour.pdf|200px|middle]] | ||
| + | |||
| + | [[File:Dataset-2-telegrams-per-weekday.pdf|200px|middle]] | ||
| + | |||
| + | == Licence == | ||
| + | All figures are licensed under the Free Culture License CC BY-SA 4.0 (see [https://creativecommons.org/licenses/by-sa/4.0/] for more infos). | ||
| + | |||
| + | <gallery mode="packed" widths=80px heights=80px> | ||
| + | File:Cc.large.png|CC | ||
| + | File:By.large.png|BY | ||
| + | File:Sa.large.png|SA | ||
| + | </gallery> | ||
Latest revision as of 14:05, 6 December 2018
Here are some more detailed figures for the paper "Using machine learning to find anomalies in fieldbus networks":
Contents
Dataset 1 - Denial of Service Attack
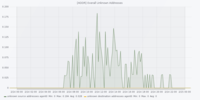
The figures are in the following order: Entropy Analyser | Local Outlier Factor Analyser | Overall Outliers | Support Vector Machine Analyser | Telegram Count | Unknown Address Analyser
Dataset 1 - New Device Attack
The figures are in the following order: Entropy Analyser | Local Outlier Factor Analyser | Overall Outliers | Support Vector Machine Analyser | Telegram Count | Unknown Address Analyser
Dataset 1 - Networkscan Attack
The figures are in the following order: Entropy Analyser | Local Outlier Factor Analyser | Overall Outliers | Support Vector Machine Analyser | Telegram Count | Unknown Address Analyser
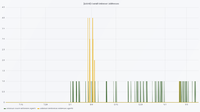
Dataset 1 - Unusual Traffic Attack
The figures are in the following order: Entropy Analyser | Local Outlier Factor Analyser | Overall Outliers | Support Vector Machine Analyser | Telegram Count | Unknown Address Analyser
Dataset 2 - Analysers
The figures are in the following order: Entropy Analyser | Local Outlier Factor Analyser | Overall Outliers | Support Vector Machine Analyser | Telegram Count | Unknown Address Analyser
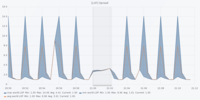
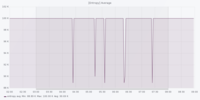
Dataset 2 - Log Analysis
In the following two pdf-files a distribution of telegrams over time (weekday and hour of the day) can be found:
File:Dataset-2-telegrams-per-hour.pdf
File:Dataset-2-telegrams-per-weekday.pdf
Licence
All figures are licensed under the Free Culture License CC BY-SA 4.0 (see [1] for more infos).